Disrupting the Cloud and Mobile Market for Frontline Work
Android Device Management for Frontline Workers
Cloud Android MDM
Built on Android Enterprise
Interactive Dashboards
Pay as you go
Your Eyes on the Frontline
Instant collection and processing of Frontline Data using Images & Voice powered by AI

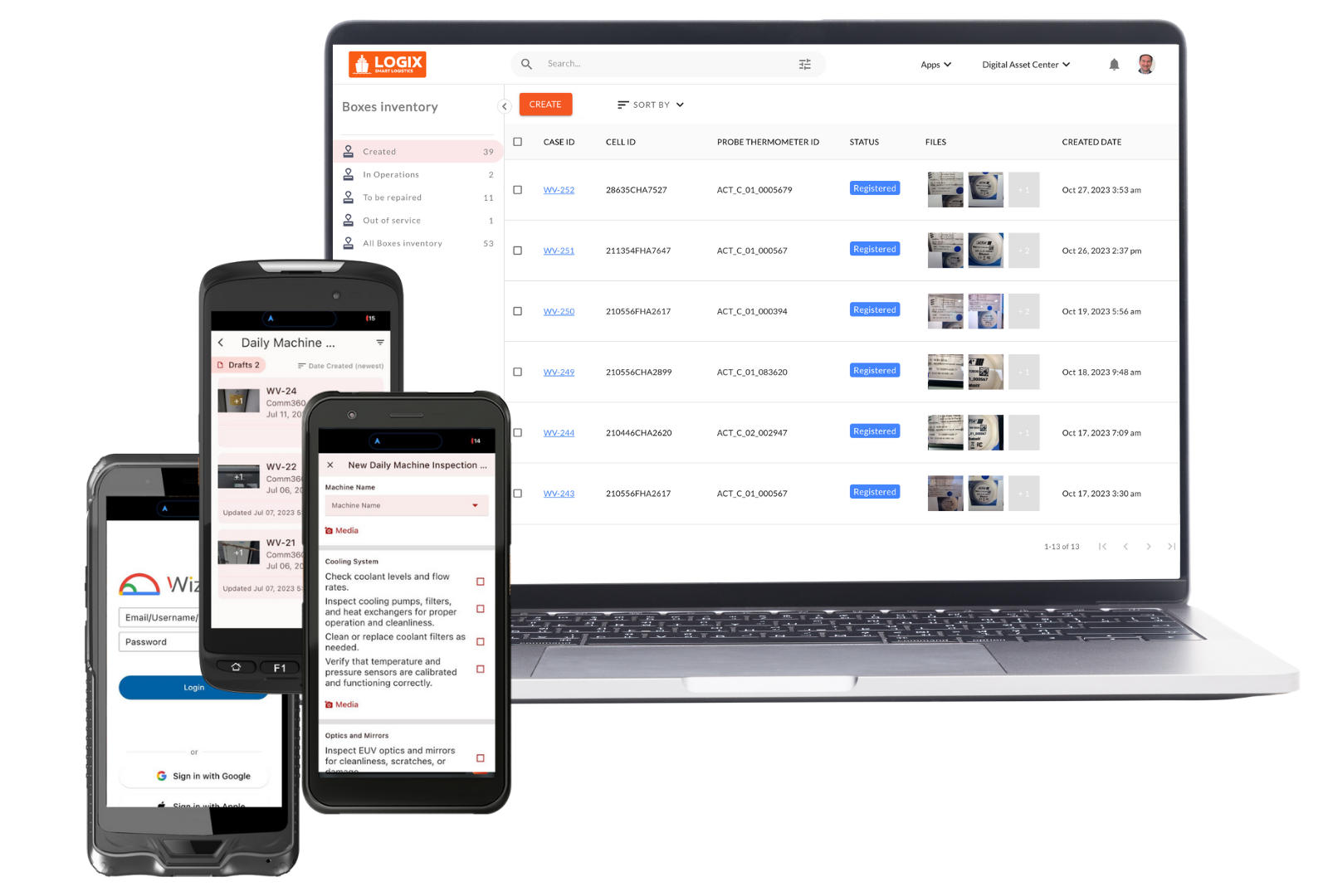
Building Intelligent Applications and Data Driven Platforms
Cloud and Mobile Apps
We specialize in building cloud native applications using Google Cloud Platform (GCP).
Data Analytics and Machine Learning
We bring the advantages of AI and Machine Learning to real-life Enterprise use cases.
API Strategy and Management
We help enterprises build their API layer to intelligently bridge their legacy data and modern apps
Working With Knowledge, Passion, Heart & Soul
We have worked with enterprises and startups around the globe and their appreciation is our main strength .
+
Engineers
Continents
+
Customers
20+
Completed Projects
Join our happy community of wizy.io SaaS users
Our Mission
We support Frontline Workers by delivering Innovative Digital Cloud Solutions that require no code, no training and are easily usable by any standard of literacy. We enable the Frontline Worker to leverage Android Enterprise, Google Hyperscale Cloud Platform and Artificial Intelligence services to digitize their everyday work.
Our Story
Wizy is a team of entrepreneurs building B2B SaaS solutions for frontline work, on Google technologies. We work with innovative customers to develop disruptive Cloud SaaS solutions. We leverage the power of the Cloud, AI and Mobile adoption to disrupt and innovate.
We are “global by design” with founders and teams on 4 continents, as well as customers in 30 countries. Our team of Developers, QA and Customer Success associates are located in Angers France, near the “Chateaux de la Loire”, and in Manila Philippines.
Wizy was launched in September 2016 simultaneously in San Francisco, Manila and Paris by co-founders Laurent Gasser, Gino Tria and Louis Naugès. They combined their strong experiences in business, technology and markets. Louis Naugès and Laurent Gasser are repeat entrepreneurs who previously co-founded Revevol in 2007, the first GSuite partner in EMEA which brought to Google 70% of GSuite early adopters worldwide.
Wizy is Google Cloud Platform Partner and Android Enterprise Partner
Our Executive Team
Laurent Gasser
CEO
Gino Tria
VP Tech Services - Product Manager WizyVision
Florian Ponroy
CTO - Product Manager WizyEMM
Louis Naugès
Chief Strategy Officer
Lionel Marcialis
COO WizyVision
Scott Beachley
General Counsel
Herminio Marquez
General Manager - LATAM & IBERIA
Our Management Team
Melissa Tria
Director QA
Annette Gasser
Director Finance
Carlo Bambo
Lead Developer
Jean Nabong
Lead Developer
Lee Lopez
Lead Developer
Lâm Tran Duy
Lead Developer